Odido (ex T-Mobile Netherlands) is the largest telecom operator in the Netherlands. On February 12th, they notified the public of the breach affecting 6+ million customers. The news that customers have heard since has only gotten worse. This article will cover the timeline of events, details of the breach, and the scale of impact.
Timeline
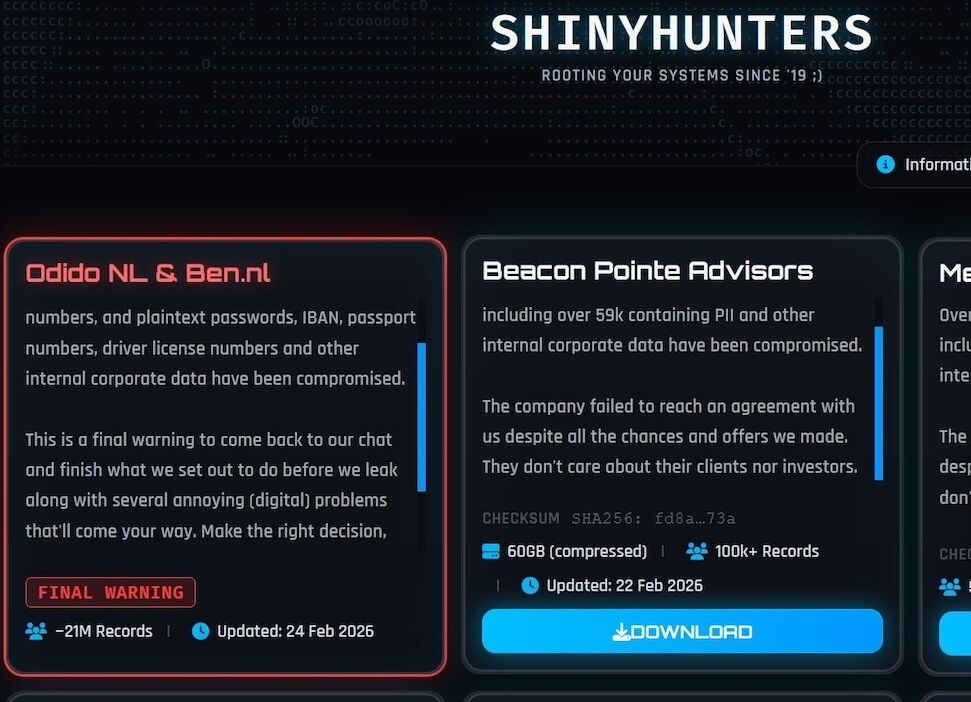
February 7th or 8th:The hacker group ShinyHunters breaches Odido’s internal systems. (More on this later.)February 8th—11th:It is unclear what Odido is doing, and when or how they discover the breach. At some point during this period, ShinyHunters makes contact with them.February 12th:Odido publicly announces the breach and informs the Dutch Data Protection Authority. Personalized emails to customers are to follow.February 12th:Ben Nederland, a subsidiary of Odido, does the same.February 13th:NOS (public broadcaster), breaks the story of how the hackers gained access.February 13th—14th:Odido sends out emails to affected customers, citing what information was leaked and what wasn’t. (More on this later.)February 15th:In a move of “brilliant” PR, Odido put out a statement that customers are not (automatically) entitled to compensation because of this breach.February 17th:Financieele Dagblad (daily newspaper) breaks the story that customers who left Odido 5+ years ago were also affected by the breach, indicating that data retention laws and regulations were not properly followed.February 17th:The breach is discussed within the House of Representatives.February 23rd:In another “brilliant” PR move, Odido offers customers a 2-year vouches for the antivirus software F-Secure. The offer is only valid for current customers.
Next, the really fun stuff starts:
February 24th:ShinyHunters threaten that they will release all the data if Odido doesn’t pay up. Initially, it was €1 million, later reduced to €500,000.February 25th:Odido announces that more customer data has been leaked than previously disclosed. They don’t give any further information, leaving customers guessing.February 26th:NOS breaks the story on what kind of data was leaked: customer service notes, some of which detail very personal information and notes about customers. The hackers approached them with a 10k sample dataset.February 26th:The Dutch police issues their official advice for Odido not to pay the ransom. Odido confirms they’ve refused to pay.February 26th — March 1st:All data is dumped on the Dark Web.
How ShinyHunters Breached Odido
Of course, there’s always a little bit of phishing involved. No AI; nothing fancy. In fact, it is the most boring, uninteresting hack you could possibly imagine.
Here’s how it went down:
- The hackers sent phishing emails to individual customer service employees to steal their login credentials (usernames/passwords) for Odido’s customer management system.
- However, they couldn’t get anywhere without bypassing multi-factor authentication. To do it, they called the employees they were trying to breach and posed as Odido’s own IT department. They convinced them to approve a fraudulent login attempt!
- Once in, they went straight towards the internal Salesforce CRM suite, and they scraped the data via automated scripts.
As an aside, this group is very well known for breaching Salesforce installations. It makes up the bulk of their most successful hacks. See more.
A Known Attack Vector
NOS.nl confirmed that the supplier of the CRM software had previously warned Odido about this exact attack method. Information on how to prepare for it was shared with the company. NOS.nl also speculated that the customer support agents who were hacked were working in an offshore, foreign call center.
What Was Stolen?
Odido communicated two things in their initial disclosure:
- In their initial announcement, they said what kind of data was included in the breach (general scope)
- Then, in emails sent out to individual customers, they clarified which data was and wasn’t included (personal scope)
It seems neither of these communications was the full truth. It is not clear whether that was because Odido was unaware or because they intentionally misled the public and their customers. As you can see in the timeline, the day after the ransom offer was delivered, Odido decided to share more about the data they previously missed. To my knowledge, they only provided that general note. They did not follow-up with individuals regarding the new category of data.
Scope of Stolen Data
- Full name, address, place of residence
- Mobile phone number
- Customer number (internal)
- Email address
- IBAN (bank account number)
- Date of birth
- Passport or driving licence (rijbewijs) number and expiry date
- Citizen service number (BSN, burgerservicenummer). This is a unique personal number issued to every Dutch resident. Not as bad as stealing an SSN in the US, but it’s still pretty damn bad.
- Residence permit details
This data was not available for every single customer in the database. Some people were luckier than others, but in the worst case, the above is the full scope of impact.
It has been explicitly confirmed that no passwords, document scans, call/SMS records, or billing details were included in the CRM data.
Additional Data
The data category that was disclosed later is the internal customer service notes. Doesn’t sound so scarry, but it turned out to be a real horror story. Within these free-text field and flags, service representatives have built a collection of extremely personal data points on individuals.
Some examples: notes on a customer having employment/financial issues, notes on a customer’s debt, notes on scams that a customer has been a victim of, and notes regarding a customer being a victim of domestic violence or stalking.
Odido’s Biggest Failures
To summarize:
- They kept data of ex-customers as far back as 10 years.
- They kept more data than was required.
- They let employees enter PII data into customer service notes, without any good PII controls in place.
- They did not have any reasonable access/data guardrails on their CRM.
- They did not communicate the full scope of the breached data until NOS.nl broke the news.
We can also assume, somewhat safely, that they did not offer proper security training to all staff members.
GDPR and Consequences
Investigations are still in progress. I expect Odido has a lot of questions to answer. Based on my layman’s understanding of GDPR, Odido may have broken quite a few articles:
- Article 5(1)(c) — Data Minimisation
- Article 5(1)(e) — Storage Limitation
- Article 25, Data Protection by Design and by Default
- Article 32, Security of processing
The result of this case will set an important precedent for future high-profile cases. Hopefully, the regulators will not miss the mark here: Odido must be held responsible, and they must face heavy fines. The country’s largest telecom provider has failed to implement and audit some of the most basic IT General Controls.
To everyone affected, I urge you to check your exposure via Mozilla Monitor and HaveIBeenPwned. Stay alert to phishing and never share your password or MFA codes with anyone.
Oh, and don’t skip corporate training videos, I guess?
Stay safe,
—Filip